Dan’s recent article referencing the Chad Daybell/Lori Vallow trials makes some excellent points, and one of them is how the Church council system helps moderate and focus leadership, especially how the seniority system acculturates any Prophet-President into this system to moderate any cult-like behaviors that we do see in certain Evangelical and even non-Christian communities. (See: James Jones’ People’s Temple, Heaven’s Gate, Antifa—all “secular” religious cults, in my opinion.) But there was an additional point that occurred to me when I was talking with a friend this morning who was closely following the trial.
Continue reading “Another Advantage of Church Government”Author: Jeff
Memory, Prophetic Translation, and the Lost 116 Pages
I am unfortunately at an advanced enough age that I have now encountered more than once something I have said, done, or written, that I have no memory of at all. This is a humbling experience. So while I was reading Kent Jackson’s excellent book Understanding Joseph Smith’s Translation of the Bible that Joseph Smith translated some sections of the Bible more than once, apparently having forgotten that he already had done so previously with a different scribe.
How do his second pass translations compare to the first? Did he translate the passages in exactly the same way?
Continue reading “Memory, Prophetic Translation, and the Lost 116 Pages”My Answer to Ellen
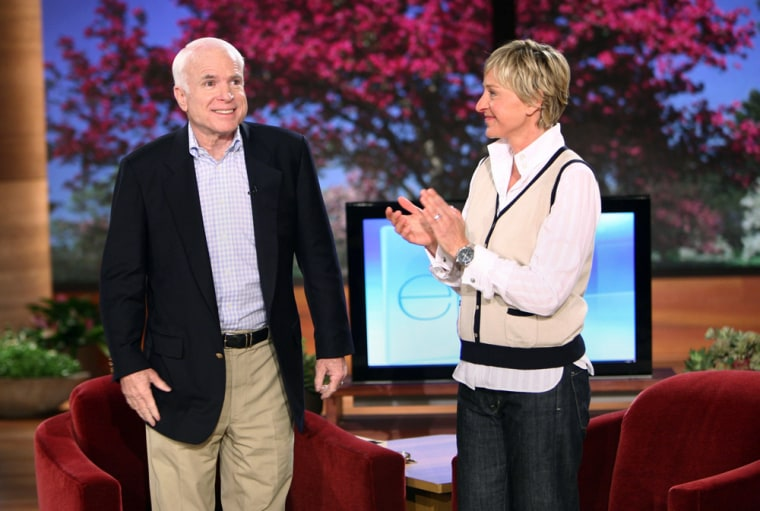
In 2008 John McCain appeared on the Ellen show and gave an awkward and inarticulate answer when challenged about her own desire to be legally married. (This is before the Supreme Court required states to recognize same sex marriage). In a blog that is long since defunct, I posted my own imagined response to Ellen if I was interviewed on her show. I reproduce it here for historical interest.
Responding to the SL Tribune’s Mischaracterization of my Testimony on Conversion Therapy

A recent article in the Salt Lake Tribune unclearly characterized my comments to the Utah State Legislature on August 18 regarding conversion therapy. I would like to clarify them. While I oppose the current version of the conversion therapy rule, I do not support conversion therapy. As a therapist, I don’t believe changing sexual orientation is an appropriate goal in therapy. But I oppose the conversion therapy rule because not only does it forbid these kinds of attempts to change sexual orientation, but also brands a much broader range of interventions as “conversion therapy,” including assisting clients who wish to manage their sexual behaviors.
Continue reading “Responding to the SL Tribune’s Mischaracterization of my Testimony on Conversion Therapy”A Reminiscence: Gospel Unity in a Time of Bitter War
What I learned from one member in Belgium about gospel unity in a time of war.
In the summer of 1990, I was serving in Liege, a French-speaking city in Belgium. As part of our work we were visiting all the members we could find on the membership rolls. One day we found an elderly sister who had joined the Church as a young woman shortly before World War I broke out, due to her age she rarely attended meetings anymore. I don’t recall if this member was living in Liege at the time of the Great War, but German atrocities were notably severe in this area, in part because this area was thwarting the achievement of a key component of the German Army General Staff’s Schlieffen Plan for winning the war.
She told me an amazing story about how the gospel of Jesus Christ can transcend bitter divisions and deep wounds.
Continue reading “A Reminiscence: Gospel Unity in a Time of Bitter War”
Information Security and the Temple Endowment
For about twelve years I worked information security for a few different software companies. We sold our software to companies and government agencies concerned with making sure those accessing their sensitive systems were (a) who they said they were, and (b) only accessing information they should have access to. The first concern is called authentication (“are you who you say you are?”), and the second one is called access control (“do you have access to the information that you need and are you denied access to the information you shouldn’t have?”). Solving these two problems have always been a challenge. And though their implementation has changed throughout time, the solutions are basically the same.
While the temple has ancient roots, it contains features that are used in the most modern and secure computer systems.
It was only a few days after I’d completed a computer security certification when I went through an endowment session again. It occurred to me that you could look at the endowment though an information security lens and gain some valuable insights. I’ll explore some of them in this post. Some of my discussion will necessarily be oblique, and may only make sense to those who have been through themselves. I take seriously the desire to keep these things sacred, and I hope my post here will be in harmony with that.
Continue reading “Information Security and the Temple Endowment”